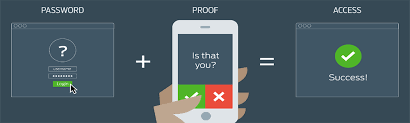
In this article will explain about 2FA (two-factor authentication) and MFA (multi-factor authentication) and why you should care about and use it to secure yourself.
As an Admin or IT Professional or an IT user few security steps you can obviously take like; installed antivirus software, set firewall rules, implement encryption technology, and regularly run vulnerability tests. But the today’s reality is that if multi-factor authentication (MFA) is not in place, these other security measures can be bypassed as we know hackers are too advanced.
Why the password is not enough
- Study says that 95% of all web site attacks are happened due to weak passwords or stolen credentials both are hackers’ weapon of choice.
- Password theft is constantly growing due to keylogging, phishing, pharming and so on.
Authentication Factors
#1: Something you know
A classified information such as a password.
#2: Something you have
An information that you can physically carry with you such as a smart card.
#3: Something you are
You must be familiar with this one an information such as a fingerprint or other biometric method.
Two-Factor vs Multi-Factor
I think the difference between both the Two-Factor Authentication (2FA) and Multi-Factor Authentication (MFA) is not as much to understand and should be already clear by now: 2FA is nothing more, nothing less than an implementation of multi-factor authentication which requires two different factor types from those listed above. Three-Factor Authentication (3FA) is also a type of MFA which requires all the three factors identified above.
Multi-Password Authentication
Don’t be confuse between Multi-Password Authentication (MPA) mechanism and 2FA and MFA mechanisms. The Multi-Password Authentication (MPA) require the user to insert multiple sets of credentials (like; different usernames/passwords) in order to access a specific resource.
Authentication vs Authorization
Both are different, but really important to understand what makes differ Authentication and Authorization. Under Authorization process; we could say that the purpose of authorization is to confirm that the requesting user is allowed to have access to the action they want to perform. In other words, while authentication is about who he is, authorization is about what he’s allowed to do. In simple words the term authentication refers to any process of verification that someone.
1 thought on “Multi-Factor and 2-Factor Authentication (2FA) and why you should use it.”
Comments are closed.