If you start getting large number of failed login attempts then it could be an indication of a security thread.
Also check what are the common root causes of account lockouts which help you to get in more detailed.
Here we will see the steps to troubleshoot this issue.
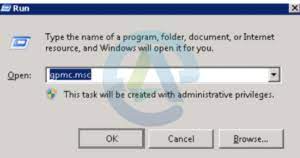
Step 1: First you have to run gpmc.msc to Configure Group Policy Audit Settings
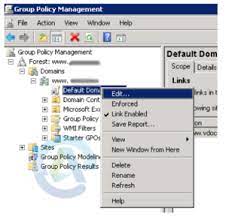
Step 2: Then you have to edit domain’s Default Domain Policy which is in the Group Policy Management Editor.
Step 3: Now you have to expand computer configuration->Windows Settings->Security Settings -> Local Policies -> Audit Policy and then double-click ‘Audit logon events’.
Step 4: After that in the Audit logon event properties, you have to select the Security Policy Setting tab and select Success.
Step 5: Now open command prompt and then run the command gpupdate/force to update Group Policy.
Step 6: To get in detailed about the failed logon events, filter the Security Event Log for Event ID 4625.
Step 7: Now double-click on the event to see details of the source from where the failed logon attempts were made.
Windows Event ID 4625: An account failed to log on
From security point of view we can say that this is a useful event because it documents each and every failed attempt to logon to the local computer apart from this logon type, location and type of account.
Get in detailed here: https://www.ultimatewindowssecurity.com/securitylog/encyclopedia/event.aspx?eventID=4625
For more information, please refer to the following links:
How to Troubleshoot Account Lockout in Active Directory
Common Causes for Account Lockouts – Resolution and Troubleshooting Steps